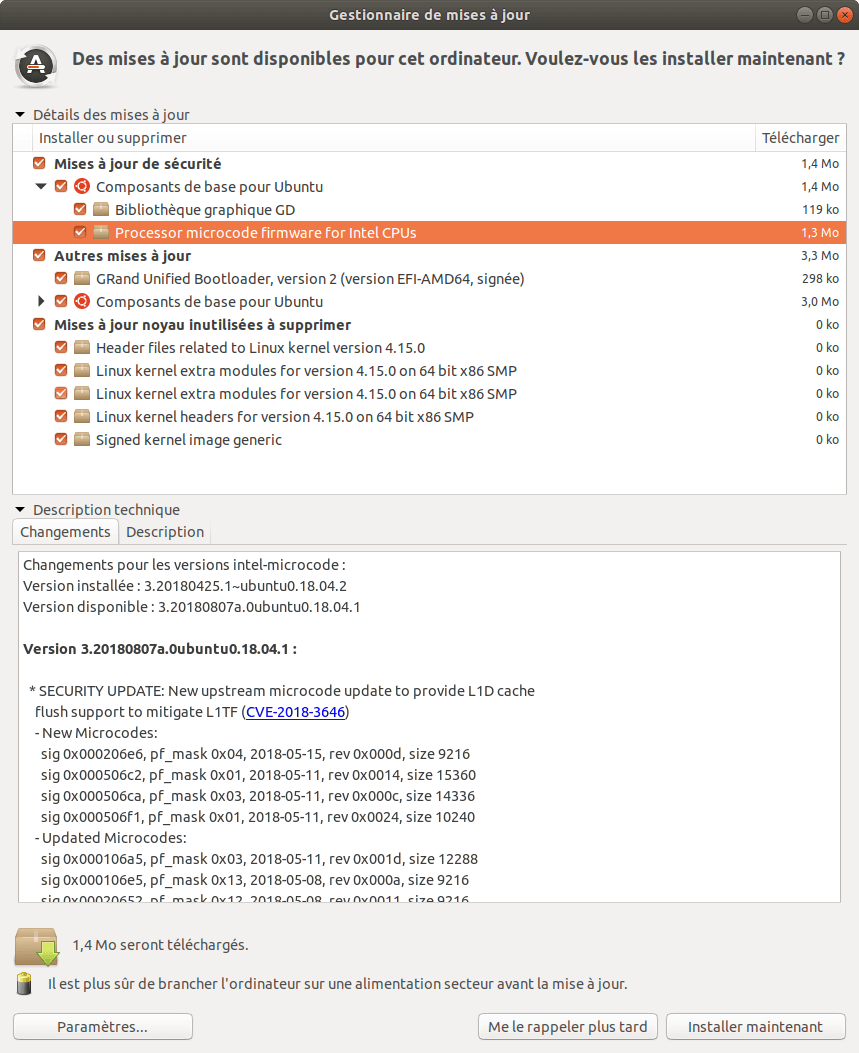
Ubuntu a mis en production aujourd'hui les microcode pour corriger "Speculative Store Bypass" (CVE-2018-3639)Avant la mise en production de ces micro-code (il y a eu une longue période de validation), la mise à jour de l'UEFI était nécessaire.
 Avant la mise à jour :
Avant la mise à jour :$ dmesg | grep microcode
[ 0.000000] microcode: microcode updated early to revision
0x2d, date = 2018-02-07[ 1.336839] microcode: sig=0x206a7, pf=0x2, revision=0x2d
[ 1.336990] microcode: Microcode Update Driver: v2.2.
$ grep "" /sys/devices/system/cpu/vulnerabilities/*
/sys/devices/system/cpu/vulnerabilities/l1tf:Mitigation: PTE Inversion; VMX: conditional cache flushes, SMT vulnerable
/sys/devices/system/cpu/vulnerabilities/meltdown:Mitigation: PTI
/sys/devices/system/cpu/vulnerabilities/spec_store_bypass:
Vulnerable/sys/devices/system/cpu/vulnerabilities/spectre_v1:Mitigation: __user pointer sanitization
/sys/devices/system/cpu/vulnerabilities/spectre_v2:Mitigation: Full generic retpoline, IBPB, IBRS_FW
Après la mise à jour :$ dmesg | grep microcode
[ 0.000000] microcode: microcode updated early to revision
0x2e, date = 2018-04-10[ 1.332247] microcode: sig=0x206a7, pf=0x2, revision=0x2e
[ 1.332451] microcode: Microcode Update Driver: v2.2.
$ grep "" /sys/devices/system/cpu/vulnerabilities/*
/sys/devices/system/cpu/vulnerabilities/l1tf:Mitigation: PTE Inversion; VMX: conditional cache flushes, SMT vulnerable
/sys/devices/system/cpu/vulnerabilities/meltdown:Mitigation: PTI
/sys/devices/system/cpu/vulnerabilities/spec_store_bypass:
Mitigation: Speculative Store Bypass disabled via prctl and seccomp
/sys/devices/system/cpu/vulnerabilities/spectre_v1:Mitigation: __user pointer sanitization
/sys/devices/system/cpu/vulnerabilities/spectre_v2:Mitigation: Full generic retpoline, IBPB, IBRS_FW